serving hattiesburg and the surrounding area.
(columbia, petal, purvis, sumrall, laurel, USM, jcjc, jones county, lamar county, forrest county)
UPDATED!!!! *
i’ve had a plague of spam, junk email in the past couple of years. i use mozilla thunderbird as my regular email client IMAP. mozilla offers a spam or junk mail solution in the for of a tool known as spamassassin. this tool works when your computer accesses your email on whatever time frame you set for it to check for new emails. once the email passes through the tool, it will hopefully flag many or most spam emails. the tool also seems to get better the more you interact with thunderbird, marking those things that slip through as spam. from what mozilla says, the tool begins to learn what is spam to you.
there are a couple of holes with this method and i wanted to write a blog post to show what i’ve done to fill in these holes. maybe start some dialogue with a few of you that are more knowledgeable and maybe we can share some information, while others may find this helpful.
for most people, they use gmail, or yahoo, or hotmail as their one and only email. other’s have one for serious use and another to use as a throwaway for things that they don’t really care about but have required them to give out an email. it seems once your email gets to that wrong place, then it gets distributed to the spammers and then you just can’t keep up. and most people give up. check out my wife’s email inbox notifications. 7323!!! if you have more, post a snapshot below. let’s see who has the record. we are being inundated with spam snail mail in our mailbox, spam and junk emails and spam in the form of robocalls or telemarketers with phone calls.
i don’t know about you, but that number bugs me. i would keep wondering what emails have i missed. for one thing, most of my emails are for business and i have different ones set up for my vendors, accounts, general public inquiries, and personal ones, etc. i have my own website, so i can make as many emails as i find necessary. so this post is mainly for those of us that maintain our own website and have access to our email portals online. i recently tried this with my gmail account and found it to be working so far. this post is not meant to have all the answers and i surely don’t, as this information was tailored specifically for my own hosting provider and places i found my spam to be coming from. your list may be different. this is constantly changing, so maybe over time, we can pool our list and create a evolving master list.
so back to spamassassin. since my iphone also accesses my email, sometimes my mail will pull down before it can reach spam assassin. most of us have our phone with us all the time. and spamassassin is not part of the apple email process. my home computer is not always on. i turn it off when not in use. so if my phone pulls down my messages first, all my spam that i had hoped to try to filter with mozilla thunderbird spamassassin just didn’t happen…
soooo, what to do?
the spam needs to be stopped on the server side of things. with my web hosting, i have a portal to access my emails from the server side. this portal has tools available for setting filters. in the beginning, for the most part, i did not have any clue as to how to use these filters and i still have limited knowledge – so if you have some suggestions, please post a comment. i’m really posting this to help stay on top of this stuff and use as a learning exercise.
 once logged in, i can then access the email account options. if this looks familiar to you, then great. if not, you are on your own.
once logged in, i can then access the email account options. if this looks familiar to you, then great. if not, you are on your own.
 scroll down to email filters. at this point you have the option to create a filter. i’m using the “email filters” method instead of the “spam filters” option earlier on that list. with “spam filters” the options are limited and a blanket or shotgun approach.
scroll down to email filters. at this point you have the option to create a filter. i’m using the “email filters” method instead of the “spam filters” option earlier on that list. with “spam filters” the options are limited and a blanket or shotgun approach.
you only have the option of setting a variable threshold. very limited.
with email filters, there are more options. a little more confusing, but more options to catch what you want to catch.
the language i will be using for my filter will be using “regular expressions” also known as regex. the reason for using this type filter will become more apparent later in the post regarding snow shoe type spam.
for spam coming from mostly legitimate sites that have a .com that i really don’t want to hear from, it fairly straight forward. i will add a filter – for the filter name, i call mine “.com type spam”. rules are “any header” “matches regex” and then i list my regex. this regex is composed in such a way as to be able to add any number of websites that i need to. i then have the action set to “deliver to folder” and choose a folder – in my case i have chosen my spam folder. you can also choose to “discard the message”, “redirect to email”, “fail with message” (tempting choice),
currently, for this filter my regex list is:
[box](126.com|chinayame.com|elekworld.cn|elekworld.com|jupevendue1.com|
kanaturals.com|kickitupla.com|doptf.com|sina.com|foxmail.com)[/box]
you can copy paste in the following format: each domain needs to be separated with the vertical bar.
what i have done is taken the “from” address from my spam emails and posted them into my code. this list is shorter than the next rule i have, but works for me for the most part. when i get a new spammer, i can add them to my list.
now for the tougher spam – what is known as snowshoe spam. “snowshoe spam!!!” “what?! what is that?!!”
[quote type=”center”] snowshoe spamming is a strategy in which spam is propagated over several domains and IP addresses to weaken reputation metrics and avoid filters. the increasing number of IP addresses makes recognizing and capturing spam difficult, which means that a certain amount of spam reaches their destination email inboxes. specialized spam trapping organizations are often hard pressed to identify and trap snowshoe spamming via conventional spam filters. the strategy of snowshoe spamming is similar to actual snowshoes that distribute the weight of an individual over a wide area to avoid sinking into the snow. likewise, snowshoe spamming delivers its weight over a wide area to remain clear of filters. [/quote]
snowshoe spam is insidious. here is the difference from the normal spam we have come to hate – snowshoe spammers use a variety of subdomains instead of root domains. one of the ways i’m using regex is to stop the snowshoe spam, by blocking the TLD. here is new acronym to learn “TLD” which stands for “top level domain”.
[quote type=”center”]snowshoe senders tend to cycle through different business entities, domains and Internet infrastructure as a part of sending their email campaigns,” “certainly, the cost of domain registration is a factor when choosing things like a TLD [Top Level Domain]; however, these spammers also tend to not want to cluster their domains under any single domain registrar or TLD, so they register their domains at a variety of TLDs.[/quote]
they use many many different subdomains attached the the top level domain that you can’t keep up with the spam with normal spam filters. so my theory is to wholly block those top level domains that the spam is coming from. it’s a different kind of shotgun approach, but one i have found works very effectively.
here is an example – it’s easy and relatively inexpensive to get different emails. if you have a domain and a website, you can set up any number of emails for that website. for instance, i can have an email set up as fakeemail@mrfxr.com and then i can set up fakeemail2@mrfxr.com and so on. what i have found to have been happening with snowshoe email is that they will set up a variety of fake subdomains. such as fakeemail@fakesubdomain.domain so trying to block the TLD is almost impossible – they keep changing the subdomain which is part of the domain. so how do block the spam coming from the spam domain with all the random endless subdomains. that is where regex comes to play. don’t ask me for details, it took some time to come up with this formula, but it works. you just have to figure out the main domain that is sending spam and then add it to this list. this is the current list of offensive domains that i have encountered to date. i really don’t think that by blocking these domains – top level down – is going to cost me any business, or worry that i may have blocked a legitimate message with my shotgun approach.
so instead of a .com, .org, or .net – many spammers are using these following top level domains:
[box] .accountant .bid .biz .click .club .date .download .eu .faith .fr .glb .hk .info .invalid .it .jp .kim .link .nl .party .pl .press .pro .racing .review .rocks .ru .science .se .site .sk .space .stream .top .trade .us .ve .vip .win .xxx .xyz[/box]
so if your website is a part of any of these domains such as email@mrfxr.bid – sorry, you getting blocked – shotgun style.
so here is the rule and formula i used for the snoeshoe spam regex filter.
filter name “regex spam filter TOD other than .com”, filter rules “any header” “matches regex” and the regex is as follows:
[box]@.*\.(accountant|bid|biz|click|club|cn|co.uk|co.za|date|deliver|download|eu|faith
|fr|glb|hk|info|in.net|invalid|it|jp|kim|link|ltd|men|myspace|nl|org.uk|party
|pl|press|pro|racing|review|rocks|ru|science|se|site|sk|space|stream|top|trade
|us|ve|vip|win|website|wellsfargo|xxx|xyz)[/box]
the formula is written in such a way as to allow the regex to catch these offending domains regardless of their subdomains. you will need to copy and paste the entire formula. you can add to the formula, just keep the domains separated by the vertical bar.
so there you have it – something that may help you out. declutter your life – clean out that inbox. what are your thoughts? leave me a comment.
P.S. – oh btw almost forgot – here is what i did for gmail.
update! since writing this, another monster spam slipped through and i was able to find a block for it. at first i didn’t want to block mail coming from more legitimate domains such as .net, .org or even .uk but this whopper slipped through support@mails.tytheringtongymkhana.org.uk WHAAAA!!!! how would you block that?!
i guess it could be viewed like this: support@fakesubdomain1.fakesubdomain2.legitdomainusedasasubdomain3.legitdomain
so after much reading, what i did was to break it down to be used in the TLD regex code. the breakdown would be |org.uk| and once it is added into the regex, it will block that faked subdomain, but will still let any legit email from .org or .uk through – no worries!
so, the new updated TLD regex is:
[box]@.*\.(accountant|bid|biz|click|club|cn|co.uk|co.za|cricket|date|deliver|download|eu|faith
|fr|fun|glb|hk|host|icu|info|in.net|invalid|it|jp|kim|link|ltd|men|myspace|nl|online|org.uk
|party|pl|press|pro|racing|review|rocks|ru|science|se|site|sk|space|stream|top|trade|us
|ve|vip|win|website|wellsfargo|xxx|xyz)[/box]
also for more in depth reading on the subject, click here. if you are the author (Anna E Kobylinska) and get a bounceback to my blog post here, maybe you could give me some deeper guidance/advice. thanks!
*UPDATE
it seemed my service provider made some changes that rendered my prior formula unusable, so i had to resort to creating a new rule for each TLD that i needed to block…. what a pain.
until today!
i ended up getting in touch with maria z. at my provider who went beyond the extra mile and along with her team, helped to craft a formula that would work well with my (her) service provider with most of the TLD’s that i had compiled.
from > matches regex
([\w-]+)(?=\.(?:click|club|cricketooo|ac|accountant|agency|ar|bid|bit|biz|br|ci|cf|cc|cl|click|club|cn|cricket
|cx|cz|date|de|deliver|download|es|eu|faith|fr|fun|ga|gdn|gg|glb|gq|hk|host|icu|in|info|in.net|invalid
|it|jp|ki|kim|life|link|live|loan|ltd|me|men|ml|mn|ms|mu|myspace|nf|nl|online|org.uk|party|pl|press
|pro|pw|racing|rent|review|rocks|ru|sc|science|se|sh|shop|site|sk|so|space|store|stream|su|sx
|tech|tj|tk|to|tokyo|top|tr|trade|ug|us|uy|ve|vip|vn|win|website|wellsfargo|work|world|xxx|xyz))
discard message
she went on to add,
“However, I would like to point out that if you add the .co TLDs it will also start to block the emails from .com email accounts. This is why We have added the .co, .co.uk and the ‘jjajt.com’ ones by adding the filters with the first field configured as From and the other one to Equals.”
so after reviewing her additions, it looks like the following. 3 separate filter entries.
from > equals
.co
discard message
from > equals
.co.uk
discard message
from > equals
jjajt.com
discard message
*LATEST UPDATE!!!
seems i recently began to receive some emails from TLD .co and i forgot about the update to my post here and added .co to my filter. a few days went by and was expecting an important email and nothing was coming through, not found in spam or junk. i then remembered what i had done and pulled it out and the emails started coming through again. adding the .co TLD with my formula also started pulling down any .com TLD! yikes. but i ran across some information that helped me out.
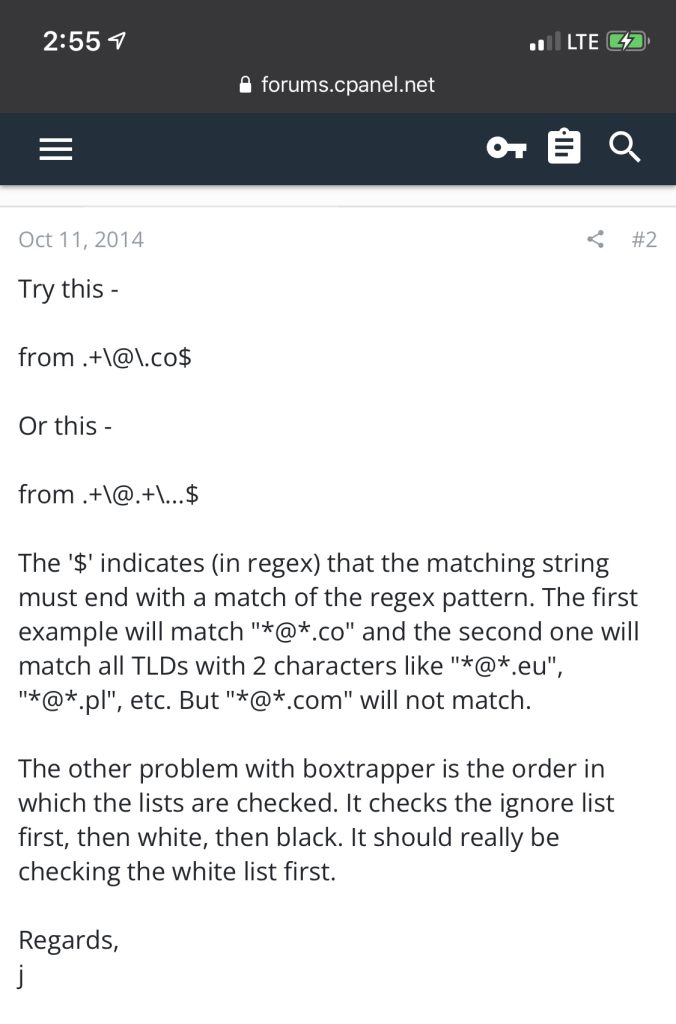
so i added .co| to my long formula along with the $ sign.
looks like this: .co$|
also found a great email regex tester, you can test my newest formula out here for yourself.
another update 3/21/22 – this .co TLD is a huge pain. even with the very capable regex, i was still getting some trash from this TLD .co – when testing my latest regex with some of these spam emails, my tester showed that it was indeed triggering, but it would somehow still come through. i don’t know how this could happen. if the regex was true, it should be dumping these emails to trash, but it was still coming through. we did some additional tests – one where i stopped getting any emails at all (it wasn’t a good regex, was catching all .com emails as well as .co) but we came across another one that seems to be working at the moment. i need to study the structure to better understand how this is working, but it is working well.
from matches regex (?:\Wco\W) discard message – tested with https://regexr.com/
[…] and have my own emails such as ****@mrfxr.com and i tend to have gotten lots of spam and i’ve managed to block a lot of it using the method described in this post. but i imagine that many of you are using gmail, yahoo, etc and they are very good for the most […]